Member-only story
Threat Detection in AWS
As more and more companies start to adopt cloud services to enable remote work and reduce the need for on-prem solutions more and more attackers are starting to target cloud environments. Since cloud is still relatively new a lot of companies make simple mistakes that enable attackers to easily steal sensitive information or pivot from cloud infrastructure to internal applications/systems. As these attacks started to increase cloud providers started to offer solutions to natively detect possible malicious activity within the cloud environments. A reasonably good solution by AWS is GuardDuty.
“Amazon GuardDuty is a threat detection service that continuously monitors for malicious activity and unauthorized behavior to protect your AWS accounts, workloads, and data stored in Amazon S3". The service is not free, however, its a great way to quickly increase threat detection capabilities within your AWS environments.
What does it detect?
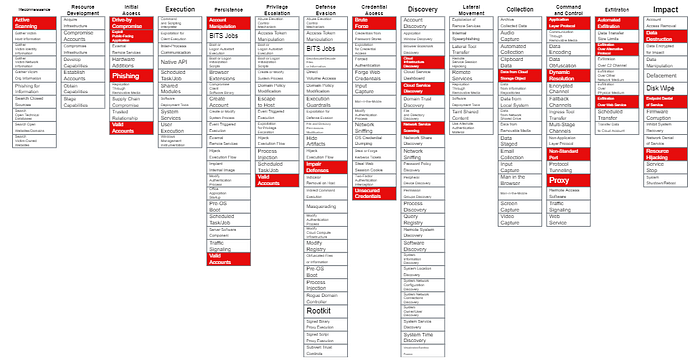
GuardDuty, at the time of this writing (8/2021), has 74 unique signatures/detections ranging from low severity alerts that will alert you when a CloudTrail logging policy has been disabled to more severe alerts that can alert you to backdoor behavior/C2 traffic. A full list of the detections can be found HERE. A useful github repo conveniently maps these detections to MITRE (found HERE). An example of the MITRE Navigator output is seen below.
While the coverage via GuardDuty is significant I don't recommend solely relying on this service for threat detection within your AWS environments. However, for organizations without dedicated threat detection developers this is a great starting point. The remainder of this article will assume you’re sending GuardDuty logs into your SIEM and will provide a few examples of threat detection ideas that can compliment your GD alerts.
Instance Created by New User
This detection would alerts analysts to suspicious activity in which a newly created user runs/creates a new instance within a short period of time. This detection is designed to pick up when an attacker already acquired access to an IAM account, but, has created a new account to preform their additional actions on objectives. The time between when the user is created and an instance is run with that new…
